In this article, we will examine two papers related to the topic of anonymity in e-participation: Ruesch & Märker 2012 – “Making the Case for Anonymity in E-Participation” and Moore 2016 – “Anonymity, Pseudonymity and Deliberation: Why Not Everything Should be Connected.” Our focus is on the concept that there may be an optimal solution in the anonymity spectrum, which strikes a balance between conflicting properties at both ends.

In this article, we will examine two papers related to the topic of anonymity in e-participation: Ruesch & Märker 2012 – “Making the Case for Anonymity in E-Participation” and Moore 2016 – “Anonymity, Pseudonymity and Deliberation: Why Not Everything Should be Connected.” Our focus is on the concept that there may be an optimal solution in the anonymity spectrum, which strikes a balance between conflicting properties at both ends.
Advocating for Anonymity in E-Participation
We will examine the points raised in the first paper, which presents an analysis of the participatory budget of the city of Gütersloh in Germany. Although the title may suggest a stance in support of anonymity, it is important to note that the concept of anonymity is not absolute and exists on a spectrum. This spectrum is where the trade-offs between opposing arguments take place. The discussion is relevant to various online platforms such as forums, social networks, and the web in general, and therefore, we will first review general points.
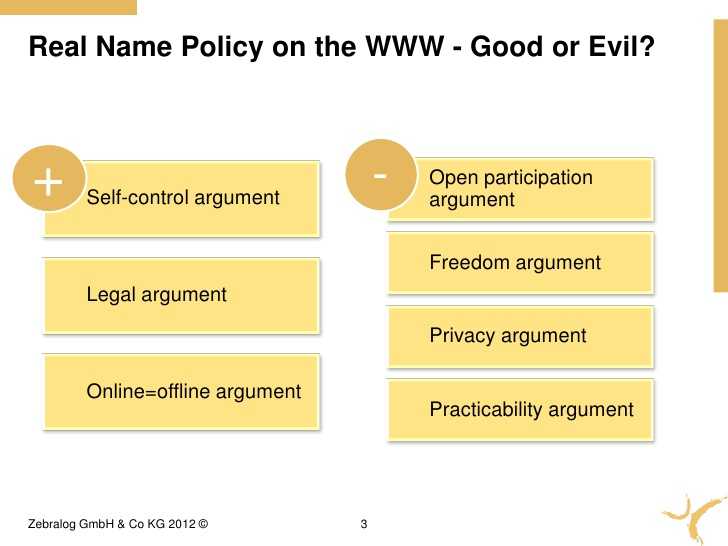
General arguments
- The self-control argument
There is substantial evidence supporting the argument that anonymous communication often leads to more uncivil discourse, while a real name policy can promote more civilized communication. The ability to be identified by others appears to foster self-restraint, reduce personal attacks, and help establish “communities of trust.”
- The legal argument
Advocates of the real name policy emphasize the significance of having easily identifiable profiles to ensure legal accountability for the actions and language used by internet users.
- The online=offline argument
If we are expected to be accountable using our real names in our offline lives, why should we not have the same expectation in our online lives?
Conversely
- The open participation argument
Requiring users to disclose their real name could lead to the exclusion of many individuals from participating in forums or social networks, particularly in authoritarian regimes where those critical of the government may face repercussions.
- The freedom argument
Users are more likely to express themselves freely and without being influenced by groupthink when they are not required to disclose their real identity.
- The privacy argument
Users should have the right to choose whether to make certain political or other opinions publicly accessible, especially considering that information once published on the internet can be almost impossible to control.
Arguments specific to E-participation
Many of the points discussed so far are likely familiar as they relate to observations made in the previous post. However, the focus has mainly been on social networks and unmoderated online forums, leaving the area of e-participation relatively unexplored in regards to anonymity and real name policy. This paper aims to fill that gap by explicitly connecting the “anonymity debate” to e-participation, presenting both pros and cons as rationale and objections, respectively.
Rationale 1: Requiring a real name policy and personal data can ensure that only eligible citizens participate, thereby improving representativeness and, in turn, legitimacy.
Rationale 2: Requiring users to disclose their real name and personal data ensures that the quality of dialogue is improved by preventing offensive comments from anonymous users.
Rationale 3: The following objections challenge the points made in favor of real name policy and the request for personal data in ensuring transparent communication and strengthening democracy:
Objection 1: The focus on real name policy and request for personal data can detract from discussions centered on issues, leading to a biased perception of messages that degrades the quality of discourse.
Objection 2: Real name policy and request for personal data infringe upon individuals’ privacy rights.
Objection 3: Requiring a real name policy and personal data can lead to time-consuming and costly administrative issues.
Objection 4: Real name policy and request for personal data can lead to negative media attention and public perception due to legal, administrative, and usability problems they cause.
Objection 5: Requiring real names and personal data may create usability issues that discourage people from participating, ultimately leading to a decrease in overall participation.
The arguments put forth regarding online discussion and the internet at large share a considerable amount of common ground with those presented in the case of e-participation. Rationale 2 and Objection 1 align with the general arguments for self-control and quality, while Objection 2 corresponds with the broader arguments for open participation and freedom.
Preserving Integrity through Pseudonymity
Introducing Integrity Preserving Pseudonymity as a Compromise Solution:
The authors of the paper argue that, based on the Gütersloh experience, the objections to real name policy outweigh the rationales. However, as we mentioned earlier, anonymity is not a black and white issue and there are various compromise solutions between complete anonymity and real name policy. These range from no registration at all to registration with verified personal data.
One potential solution that could be considered a midpoint is Integrity Preserving Pseudonymity. With this approach, citizens are required to validate their real identities to participate in the platform, but their identities remain private and cannot be linked to their pseudonyms beyond the eligibility requirement.
This compromise solution allows citizens to maintain a degree of identity by linking their contributions to their pseudonyms, but still ensures their privacy with respect to both the general public and institutional authorities managing the participation process. This strikes a balance between anonymity and real name policy, where identity is stronger than complete anonymity but weaker than real identity.
Integrity preserving pseudonymity can be established using anonymous credentials, a cryptographic technique introduced by David Chaum (CHA 85). Revisiting the pros and cons of this type of pseudonymity, we can analyze whether the Rationales and Objections support or challenge the use of pseudonymity, as well as the two extremes of pure anonymity and real names. To simplify, we have abbreviated the arguments and merged Objection 4 with Objection 3. The following table summarizes the analysis.

The cells in the table are marked with a check (√) or an X depending on whether the argument supports or questions the use of pseudonymity. Cases where the argument has both positive and negative aspects with respect to the policy are marked with both symbols. Here is a summary of the arguments for pseudonymity.
- Legitimacy, integrity
Integrity preserving pseudonymity guarantees that only eligible citizens can participate while maintaining integrity.
- Civility
Pseudonymity has characteristics of both real name policy and anonymity. On one hand, since participants are not fully identifiable, there is some possibility for uncivil behavior, which may pose a challenge for accountability. However, on the other hand, pseudonymity does offer a degree of identity through linking contributions to a particular citizen, allowing for a level of accountability. While this level of accountability is not as strong as that offered by real names, it is greater than that provided by pure anonymity.
- Communication transparency
According to the definition in the paper, the argument against pseudonymity based on the fact that citizens do not know the real person they are communicating with is considered negative. However, it is possible to make points similar to those made for civility in this context.
- Issue-centric debate
This argument is equivocal for the same reasons as described for Civility. The presence of some degree of identity may divert from a purely issue-focused discussion, similar to what happens with pure anonymity.
- Privacy, inclusion, freedom
Integrity preserving pseudonymity, by definition, protects citizens’ real identities, which in turn promotes inclusion and freedom.
- Administrative complexity
Implementing pseudonymity involves citizen authentication using their real name and other personal information, resulting in similar complexity issues to those of a pure real name policy. Furthermore, pseudonymity requires a meticulous implementation with proper cryptography, leading to administrative complexity and associated costs.
- Usability and participation
This argument presents a mixed evaluation for pseudonymity. On one hand, the real name authentication required for pseudonymity may result in complexity issues similar to those for a pure real name policy, decreasing usability and participation. On the other hand, pseudonymity offers some advantages for increasing participation, while still protecting citizens’ real identity, which aligns with the Privacy-inclusion-freedom argument.
The overall evaluation of a pseudonymity policy should consider the relative importance of each argument, rather than simply counting the pros and cons. Pseudonymity can function as an optimal balance between maintaining important properties of pure anonymity and ameliorating its drawbacks. However, the level of identity present in pseudonymity does pose a greater threat to Privacy-integrity-freedom than pure anonymity if inference attacks are conducted on pseudonyms’ linkable contributions. The paper suggests that negative effects of anonymity can be accounted for by the use of pseudonyms and moderation, and that real name policy should be avoided in e-participation projects.
Summary
In Ruesch & Märker’s 2012 paper, we examined arguments both for and against anonymity in general and specifically in the context of e-participation. We noted that anonymity exists on a spectrum and that integrity preserving pseudonymity falls somewhere in between complete anonymity and full identification. We then assessed pseudonymity based on the arguments presented and suggested that, depending on the importance of each argument, it could be an effective compromise that balances conflicting requirements in e-participation systems. [36]
References
(Chaum 85) — Chaum, David (October 1985). “Security without identification: transaction systems to make big brother obsolete”.
(Ruesch & Märker 2012) — Making the Case for Anonymity in E-Participation
[20] De Cindio, Fiorella. 2012. “Guidelines for Designing Deliberative Digital Habitats: Learning from E-Participation for Open Data Initiatives.” The Journal of Community Informatics 8 (2).
[21] Fredheim, Rolf, Alfred Moore, and John Naughton. n.d. “Anonymity and Online Commenting: An Empirical Study.” SSRN Electronic Journal. doi:10.2139/ssrn.2591299.
[22] Cho, Daegon, and Alessandro Acquisti. 2013. “The More Social Cues, The Less Trolling? An Empirical Study of Online Commenting Behavior.”
[23] Diakopoulos, Nicholas, and Mor Naaman. 2011. “Towards Quality Discourse in Online News Comments.” In Proceedings of the ACM 2011 Conference on Computer Supported Cooperative Work — CSCW ‘11. doi:10.1145/1958824.1958844.
[25] Fredheim, Rolf, Alfred Moore, and John Naughton. n.d. “Anonymity and Online Commenting: An Empirical Study.” SSRN Electronic Journal. doi:10.2139/ssrn.2591299.
[26] Davies, Todd. 2009. Online Deliberation: Design, Research, and Practice. Stanford Univ Center for the Study.
[29] Connolly, Terry, Leonard M. Jessup, and Joseph S. Valacich. 1990. “Effects of Anonymity and Evaluative Tone on Idea Generation in Computer-Mediated Groups.” Management Science 36 (6): 689—703.
[30] Flanagin, A. J., V. Tiyaamornwong, J. O’Connor, and D. R. Seibold. 2002. “Computer-Mediated Group Work: The Interaction of Sex and Anonymity.” Communication Research 29 (1): 66—93.